Threat Intelligence for Faster Defensive Action
Threat Intelligence for Faster Defensive Action
Correlate signals across web, API, email, and network environments to identify emerging threats earlier, reduce noise, and support faster defensive action across the Trafficmind protection stack
-
Cross-channel threat correlation
-
Automated protective updates
-
Evidence-backed reporting and workflow fit

Under attack?
-
Cross-channel threat correlation
-
Automated protective updates
-
Evidence-backed reporting and workflow fit
How Trafficmind Turns Signals into Defensive Action
Trafficmind Threat Intelligence helps teams collect, validate, and correlate indicators across web, API, email, and network layers so emerging threats can be understood faster and acted on with greater confidence. By turning fragmented signals into actionable intelligence, teams can improve investigations, reduce noise, and support faster defensive updates across protected services.
Threat Validation
Filter noise and validate suspicious activity so analysts can act with greater confidence.
Response Support
Use intelligence outputs to guide blocking, policy updates, escalation, and follow-on investigation.
Fraud and Abuse Insight
Identify activity linked to fraud, abuse, and malicious automation across exposed services and workflows.
Reporting and Evidence
Support internal review, customer communication, and audit workflows with clearer, evidence-backed outputs.
Operational Integration
Fit intelligence into existing workflows through APIs, exports, role-based views, and investigation-ready data.
Threat Intelligence for Detection and Response
Trafficmind Threat Intelligence helps teams collect, validate, and correlate signals across key environments, then turn those signals into clearer investigations, faster defensive action, and more confident operational response.
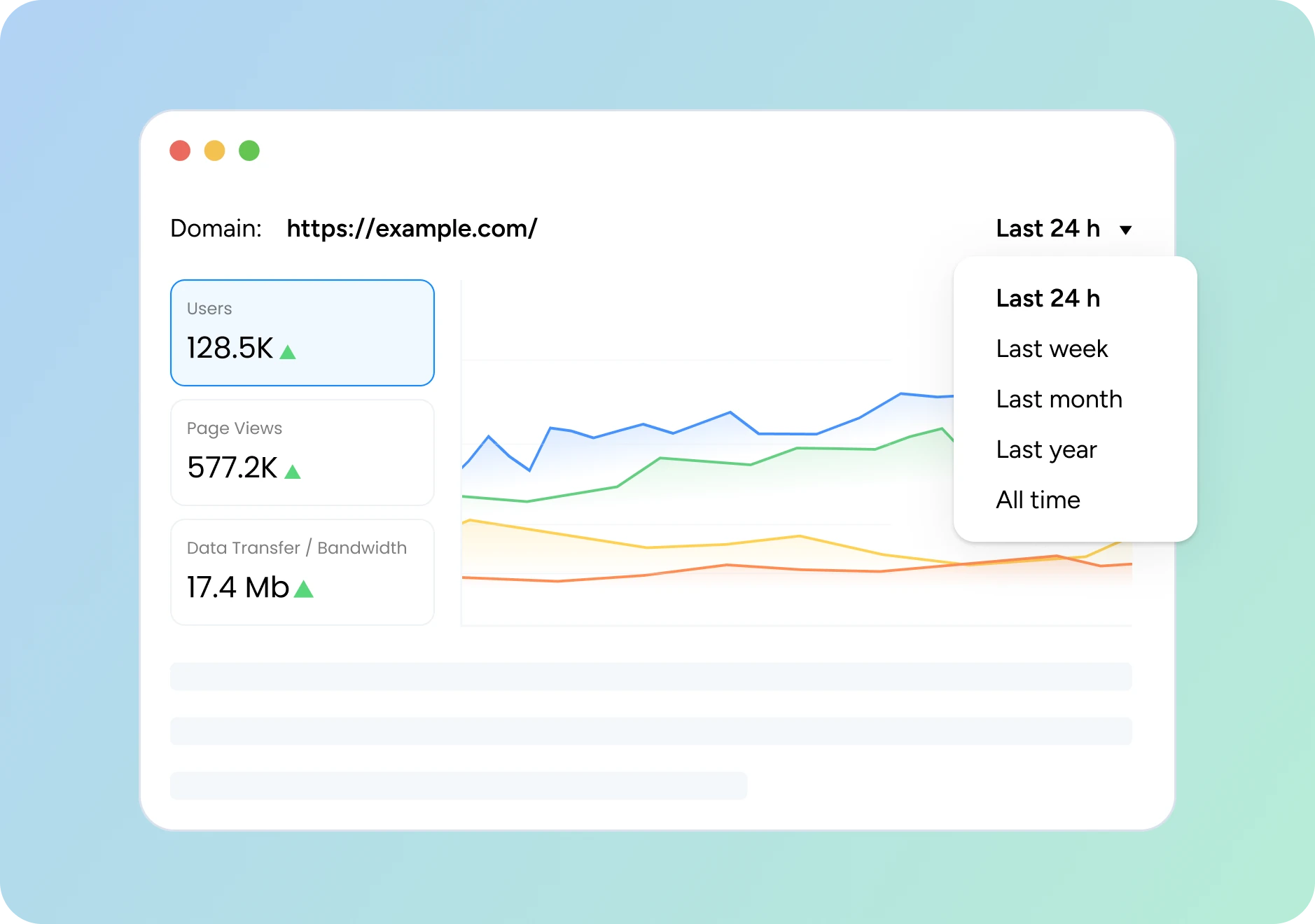
Signal Collection
Collect indicators across web, API, email, and network environments to build a broader and more complete view of active risk
Signal Validation
Use reputation, frequency, and freshness scoring to reduce noise and help teams prioritize higher-confidence signals.
Cross-Channel Correlation
Connect related attacker activity across multiple surfaces to identify broader campaigns earlier.
Edge Blocking
Stop malicious traffic and hostile behavior before threats can affect protected services..
Control Updates
Apply firewall and protection-rule updates as signals evolve to keep defenses aligned with current risk.
Operational Visibility
Use metrics, logs, and telemetry to validate changes, monitor service health, and support ongoing review.
Fraud & Abuse Defense
Reduce operational loss and customer friction by identifying activity linked to account takeover, payment abuse, and bot-driven attacks.
Incident Reporting
Document actions taken, impact, and next steps to support review, escalation, and communication.
Workflow Integration
Fit intelligence into existing operational and security workflows through exports, APIs, and role-based access.
Detect and Neutralize Attacks Before They Reach You
Trafficmind analyzes billions of web requests across our network to spot threat patterns. It detects and blocks hostile actions quickly to minimize adverse impact on your operations, revenue, and reputation.
Proactive risk blocking
Identify malicious sources and hostile behaviors before they reach networks and applications, block them at the edge, update defensive controls, and provide insights teams can act on.
Fraud and abuse defense
Trafficmind automatically detects suspicious behavior and helps stop account takeover attempts, payment abuse, and bot-driven activity across customer-facing services.
Faster incident response
Analyze signals across hosts, domains, and user devices in real time to contain threats early, then deliver reports explaining what was blocked, what changed, and what teams should review next.
Informed security investments
Use real-world attack trends and operational outcomes to guide purchasing decisions, tune priorities, and demonstrate ROI through fewer incidents, less wasted effort, and better reporting.
Verified Threat Signals You Can Trust
Trafficmind identifies potential risks and likely targets before they become active incidents by enriching, scoring, and validating signals before they are routed into investigation and protective workflows.
Anti-Phishing
Combats impersonation and malicious links
Ready to Enforce
Clear threat indicators and immediate action
Instant lookups
Real-time threat intel streamlines protection
Sector-tuned
Shows adversary patterns relevant to your industry
We use timely intelligence from trusted sources to reduce false positives and complexities, so your customers experience stable, safe services wherever and whenever they connect.
Built for Shared Security Operations and Managed Delivery
Trafficmind helps teams operating across multiple services or customer environments use correlated intelligence more consistently through centralized visibility, evidence-backed outputs, and integration-ready workflows.
- Centralized visibility across multiple services
- Signals that support shared protection workflows
- Operational context aligned with managed delivery
- Evidence-backed reporting for review and communication
Threat Intelligence for Analysis, Response, and Operations
Trafficmind combines signal analysis, response support, operational visibility, and workflow integration into a practical intelligence model for modern security teams.
Signal Handling
Collect, score, enrich, and reduce noise across multiple signal sources.
Analysis
Correlate activity across channels, surface risk trends, and improve context for investigation.
Response
Support blocking, control updates, and faster follow-on response.
Operations
Provide role-based views, exports, APIs, and audit-friendly action history.
Business Outcomes
Reduce fraud and abuse, improve decision support, and strengthen security planning.
MSSP Suitability
Support centralized visibility and shared-environment delivery models.
Why Trafficmind Threat Intelligence Is Different
Trafficmind combines cross-channel signal correlation, built-in enforcement support, and operationally usable reporting to help teams detect threats earlier, reduce noise, and respond with greater speed and confidence.
Cross-Channel Context
Correlate signals across web, APIs, email, and network activity for broader threat visibility.
Actionable Signal Scoring
Prioritize higher-confidence signals using reputation, frequency, and freshness to reduce analyst noise.
Built-In Enforcement
Connect intelligence directly to blocking, control updates, and faster protective response workflows.
Evidence-Backed Reporting
Equip teams with clear reporting, action history, and context for review, escalation, and audits.
Operational Clarity for Security Teams
Turn Threat Signals into Action