Provider-Grade Firewall as a Service
Cloud-Delivered Firewall Protection Across Layers 3–7
Trafficmind FWaaS delivers cloud firewall protection across distributed infrastructure. Inspect and control traffic across Layers 3–7 without deploying or managing firewall hardware.
-
Sub-10 ms to the edge
-
99.99% global SLA
-
Layer 3–7 policy enforcement
-
Safe rollout and rollback controls

Under attack?
-
Sub-10 ms to the edge
-
99.99% global SLA
-
Layer 3–7 policy enforcement
-
Safe rollout and rollback controls
Centralized Enforcement
Apply access controls by IP address, subnet, protocol, and port across infrastructure environments
Application Awareness
Inspect traffic at Layer 7 to enforce policies based on application behavior and request context
Protect Distributed Infrastructure Without Hardware Firewalls
Trafficmind Firewall as a Service delivers centralized Layer 3–7 enforcement across distributed environments, helping teams apply consistent policy, reduce appliance sprawl, and simplify security operations across branches, cloud workloads, and hybrid infrastructure.

Always-on protection
Trafficmind rolls out signature and policy updates using connection drains, controlled canary deployment, and automatic rollback to keep protections current while minimizing disruption to active sessions.
Low latency, high availability
Anycast routing, local points of presence, and connection pinning are designed to preserve low-latency, durable connectivity for distributed applications and user traffic, including under sudden demand shifts.
Managed operations
Trafficmind’s security team monitors threat signals, manages incident response, tunes controls, and provides reporting aligned with governance, operational, and audit requirements.
Policy-driven security
Identity-aware access policies connect users, devices, branches, and cloud environments while reducing unauthorized lateral exposure across private networks.
Cloud-Delivered Firewall Enforcement Across Layers 3–7
Trafficmind FWaaS provides cloud-delivered inspection and policy enforcement across network, transport, application, and encrypted traffic layers to help teams control access, reduce exposure, and apply consistent security across distributed environments.
Network Policy
Apply controls by IP, subnet, protocol, and port to govern connectivity across branches, workloads, services, and customer environments.
Stateful Firewalling
Use session-aware enforcement across TCP and UDP traffic to improve control over connection behavior and traffic handling.
Application-Aware Policy
Apply rules based on service and application context to improve enforcement precision across modern traffic flows.
Encrypted Traffic Inspection
Use TLS visibility and inspection to strengthen control over encrypted traffic and reduce blind spots.
DNS-Layer Enforcement
Block malicious domains, risky destinations, and suspicious resolution patterns at the DNS layer.
URL and Category Filtering
Apply web access controls using category, reputation, and policy-based filtering.
Collaborative Protection Model
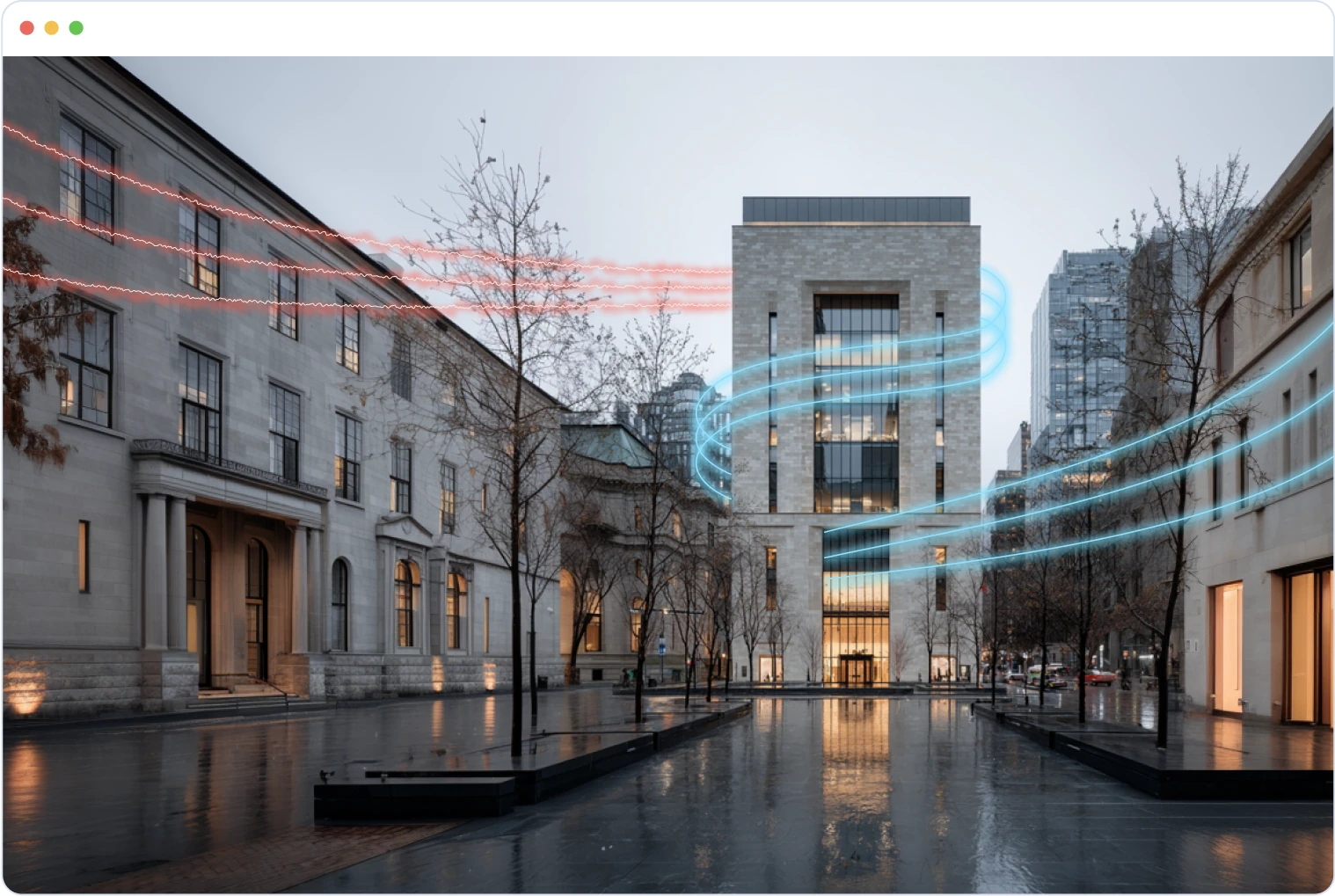
Layer-Separated DDoS Protection
Trafficmind separates traffic analysis from enforcement layers, allowing threats to be detected, classified, and mitigated across multiple stages of the protection pipeline.
Layer 7 Protection
At the application layer, behavioral analysis and machine-learning models analyze high-cardinality traffic signals using telemetry to detect abnormal request patterns in real time.
Layer 4 Protection
At the network layer, malicious packets are filtered at the header level before reaching kernel or application resources, reducing processing overhead and limiting attack propagation.
Incoming traffic
Traffic from
Traffic originating from legitimate users, automated services, IoT devices, and potential malicious sources.
Border Router
L3 filtering
Route validation, fragment filtering, and packet sanity checks block malformed or suspicious network traffic early
Secure Router
L3 and L4
Rate-limit enforcement and flood protection mitigate volumetric attacks targeting transport protocols
NGFW
L4 and L7
Traffic inspection engines apply reputation feeds, behavioral analysis, and threat intelligence policies
Security Appliance
L7 Filtering
Application-layer protection enforces WAF rules, API security policies, and OWASP-aligned controls
Clean Traffic
Validated traffic is securely forwarded to the customer’s infrastructure and services.
Inspect Traffic with More Context and Control
Trafficmind combines stateful enforcement with protocol-aware inspection to help teams identify abnormal traffic patterns, limit policy gaps, and enforce security controls across distributed traffic flows.
Transport and Session Controls
Track connection state and enforce policy across TCP and UDP sessions.
Protocol Anomaly Handling
Detect malformed or abnormal traffic behavior designed to bypass or stress security controls.
DNS and Destination Controls
Restrict access to high-risk domains, suspicious lookups, and unauthorized destinations.
Encrypted Traffic Visibility
Improve inspection coverage for modern traffic patterns protected by TLS.
Deployment That Fits Real Networks
Trafficmind FWaaS supports practical attachment models for provider networks, multi-site environments, cloud-connected estates, and hybrid infrastructure.
Global policy management
Deploy centralized firewall enforcement across modern network environments with flexible attachment options
Branch and Campus Connectivity
Apply centralized firewall policy across offices, campuses, and distributed sites.
Cloud and Multi-Cloud Enforcement
Protect workloads and egress paths across public cloud environments with consistent policy.
Data Center and Hybrid Attachment
Extend enforcement into hybrid environments where cloud-delivered policy must work alongside existing infrastructure.
SD-WAN, GRE, and IPsec Compatibility
Integrate with current routing and connectivity models while preserving operational flexibility.
Centralized Visibility and Audit-Ready Operations
Trafficmind provides the visibility and controls teams need to manage firewall policy consistently, review events, and support audit and compliance workflows across distributed environments.
Trafficmind analyzes traffic, proposes policy refinements, and quantifies their impact. Teams can apply or roll back changes in one click, export audit-ready evidence, and drill into any session to review full flow logs.
Policy Lifecycle and Change Safety
Trafficmind applies policy changes using controlled deployment methods designed to protect active sessions and reduce operational risk.

Connection Drains
Active sessions are permitted to complete gracefully when firewall policy updates affect existing flows. Connection draining reduces disruption by preventing abrupt termination of established traffic while new rules take effect.
Canary Rollouts
Firewall policy changes are validated on a limited portion of traffic before wider enforcement. Gradual rollout helps identify unintended behavior early and supports safer deployment across production environments.
Automatic Rollback
Previously stable configurations are restored automatically if a newly deployed rule introduces unexpected traffic disruption or operational risk. Rapid rollback preserves service continuity while policy issues are investigated.
Safe-Mode Bypass
Connectivity is preserved during rare policy edge cases or unexpected rule interactions. Temporary bypass mechanisms maintain availability while administrators review and correct the configuration.
Provider-Grade FWaaS Capabilities
A provider-grade capability set designed for fast technical evaluation and practical implementation planning.
Deployment Models
- Branch and campus connectivity
- Cloud and multi-cloud enforcement
- Data center and hybrid attachment
- SD-WAN / GRE / IPsec compatibility
Policy Enforcement
- Layer 3–7 policy enforcement
- IP, subnet, port, and protocol controls
- Application-aware rules
- Stateful session enforcement
Traffic Inspection
- TLS visibility and inspection
- Protocol anomaly handling
- DNS-layer enforcement
- URL and category filtering
Shared Infrastructure
- Per-customer policy separation
- Per-site rule governance
- Managed environment controls
- Structured policy ownership
- One-click rollback
Distributed Networking
- Anycast routing
- Local PoP inspection
- GRE / IPsec support
- SD-WAN compatibility
- Local breakout support
MSSP Suitability
- Centralized policy at scale
- Tenant-aware governance
- Appliance replacement / offload
Cloud & Hybrid
- Multi-cloud attachment
- VPC / VNet connector model
- Branch-to-cloud consistency
Performance & Availability
- Sub-10 ms to edge
- Low inspection overhead
- SLA-backed service
- Elastic scaling
Distributed Firewall Enforcement Architecture
Trafficmind inspects and filters network traffic across globally distributed edge nodes before it reaches protected infrastructure. Security policies are applied closer to traffic sources, helping reduce exposure while maintaining performance.
Why Infrastructure Teams Choose Trafficmind FWaaS
Trafficmind is designed for real distributed infrastructure including service provider networks, multi-site estates, cloud-connected environments, hosting platforms, and hybrid environments where centralized control, operational safety, and deployment flexibility matter.
Distributed Environments
Protect branches, cloud environments, data centers, and customer-facing infrastructure from one enforcement plane.
Deployment That Fits
Support SD-WAN, GRE, IPsec, and hybrid attachment models across different routing and connectivity designs.
Centralized Policy
Apply consistent firewall rules across sites, cloud environments, and managed infrastructure from one platform.
Safe Policy Changes at Scale
Reduce production risk with canary rollouts, connection drains, automatic rollback, and operator recovery controls.
Tenant-Aware Governance
Separate rules by customer, site, environment, or service to support safer operations in managed and shared environments.
Global Low Latency
Designed for sub-10 ms median latency to the nearest PoP across the US and Europe
Contact Us
Manage Firewall with Trafficmind